Active Directory and ADTimeline(5)
Note:I translated Japanese into English using Google Translate.
Thank you, Google.
Summary:
- Grant the access right of "AdminSDHolder" to Bob account, using DCshadow.
The nTSecurityDescriptor of "AdminSDHolder" is recorded in the ADTimeline. - The process of SDProp updates the access rights such as "Domain Admins" etc...These ACLs will now include Bob accounts.
----------
[Note]Please be aware that the verification method not be sufficient.
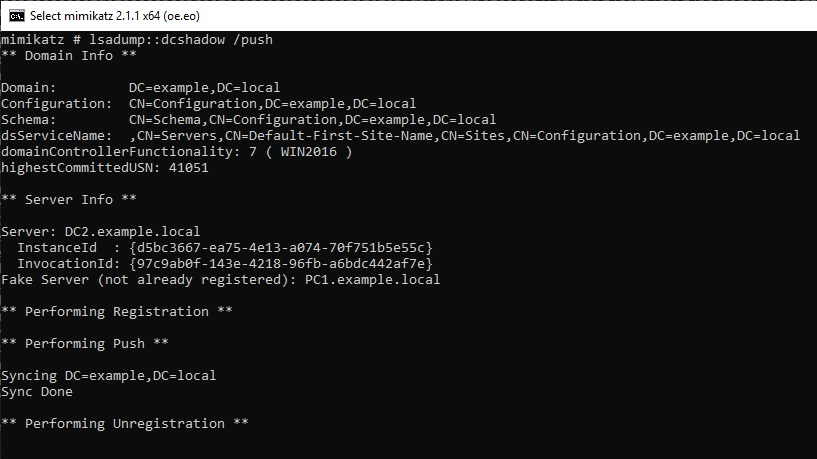
I will Check the ADTimeline of the case where changed the ACL of AdminSDHolder with DCshadow. DCshadow was executed with reference to the following URL.
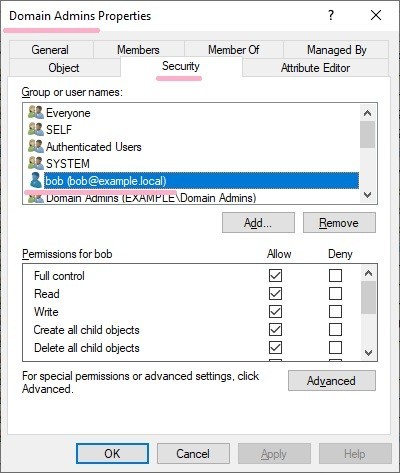
Check the ACL before running DCshadow. Bob account does not have permissions for this folder. (Bob account does not have high privilege.)

Run DCshadow and grant access to Bob account. You can confirm that the access right of the Bob account has been added.

Check the ADTimeline. NT-Security-Descriptor attribute changes and "dwVersion" value is "2".
ftimeLastOriginatingChange : 2019-03-11T07:27:01Z
Name : AdminSDHolder
pszAttributeName : nTSecurityDescriptor
ObjectClass : container
DN : CN=AdminSDHolder,CN=System,DC=example,DC=local
ObjectCategory : CN=Container,CN=Schema,CN=Configuration,DC=example,DC=local
SamAccountName :
dwVersion : 2
WhenCreated : 2019-01-20 19:19:55Z
Member :
ftimeCreated :
ftimeDeleted :
SID :
pszLastOriginatingDsaDN :
uuidLastOriginatingDsaInvocationID : d5bc3667-ea75-4e13-a074-70f751b5e55c
usnOriginatingChange : 41052
usnLocalChange : 65687
"ADobjects.xml" file contains detailed information of AdminSDHolder. I can check the ACL added to Bob account.

Wait for execution of SDProp processing.
I can check the records related to ACL change of AdminSDHolder on the ADTimeline.
Display the ACL of the Domain Admins group, Bob has full control. (also in "ADobjects.xml" file.)
PS
I checked the status of adminCount in Bob account. the "adminCount" value of the Bob account is not set.

Verification environment: Windows Server 2019 1809, Windows 10 1809, Time zone UTC
Reference URL:
www.labofapenetrationtester.com
