File System Tunneling and C:\
Note:I translated Japanese into English using Google Translate.
Thank you, Google.
Last week I enjoyed File System Tunneling.
Unfortunately, I could not reproduce File System Tunneling with NTFS 'E: drive. This time I use the C: drive for testing.
Also, last time I did not refer to the USN journal and $LogFile.
Can I find out the occurrence of File System Tunneling from the USN Journal?
Copy the owl image file to the C:\Pictures folder.
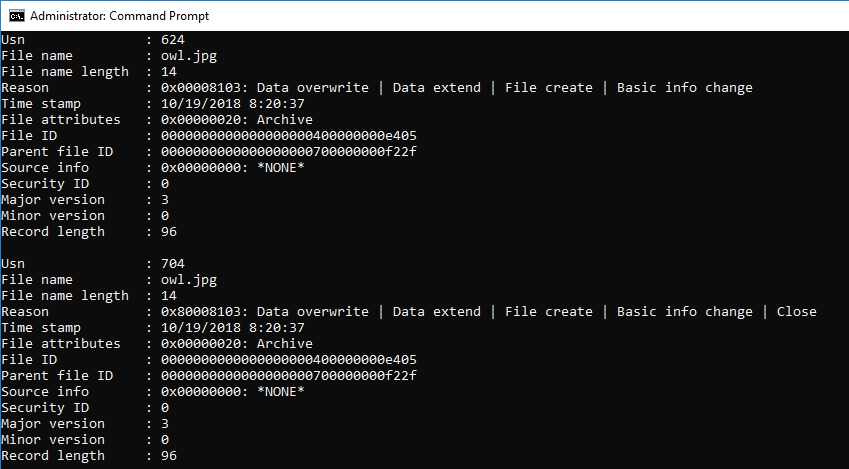
Check the USN journal and the timestamp.
>fsutil usn readjournal c:
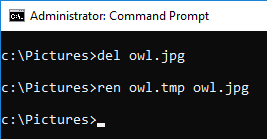
Delete the file owl.jpg and create the same file name.

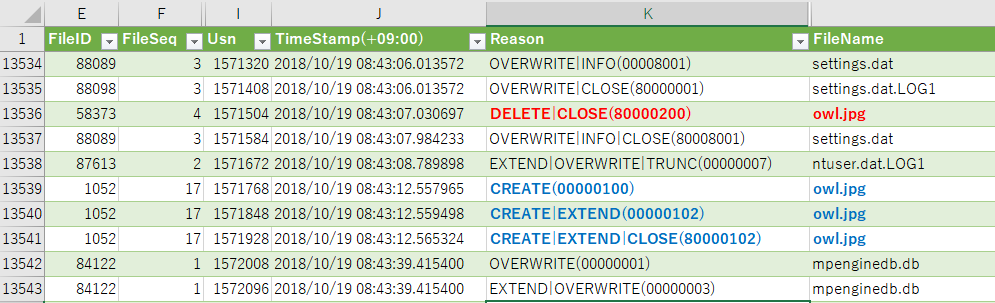
Use usn_analytics to parse the USN journal.
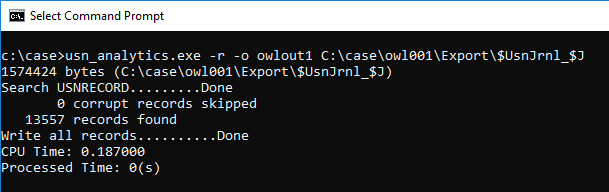
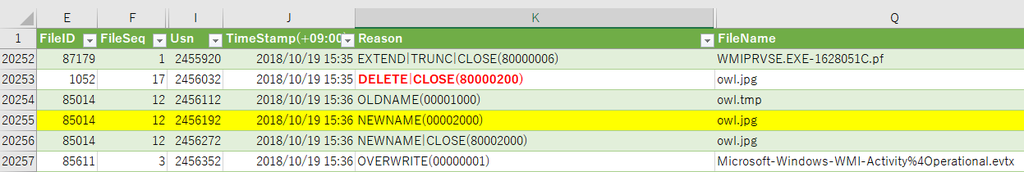
Let's check the parsing result.
I was expecting a record of "Basic Info Change", but it was not there.
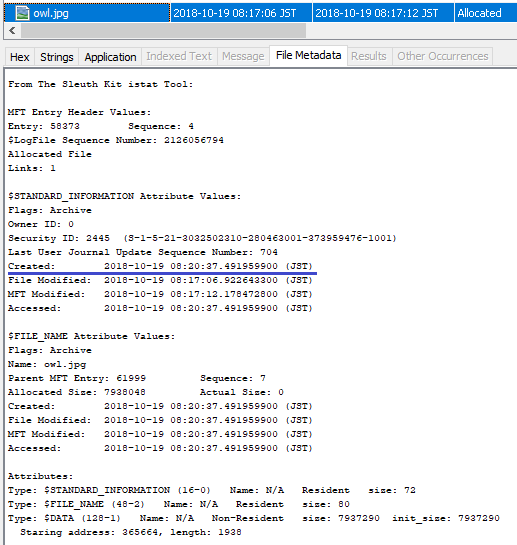
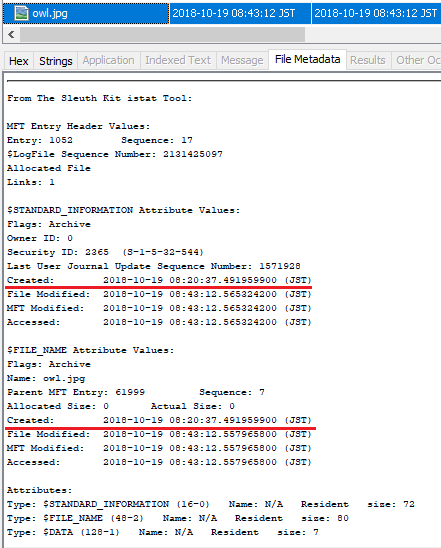
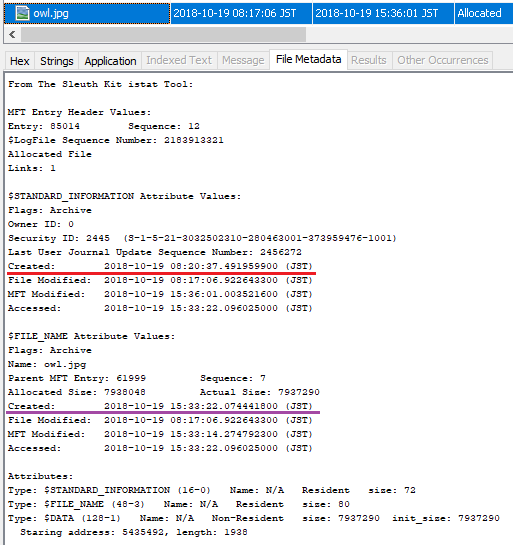
Confirm the meta information of the created file.
The timestamp of Created is restored by File System Tunneling. (Created time stamps of $SI and $FN, both have been restored.)
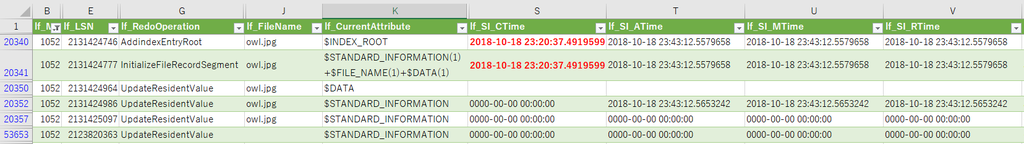
Use LogFileParser to parse $LogFile and check the record of owl.jpg.
When you confirm the InitializeFileRecordSegment, Created time stamp has restored value appeared.
Next, try changing the file name. I copied the owl.tmp file to the Pictures folder.
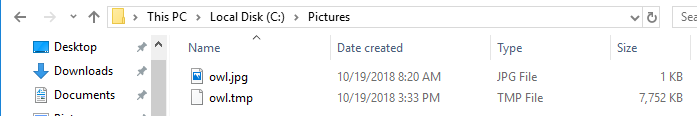
Confirm the parse result of USN journal, Basic Info Change is not recorded.
Confirm Created time stamp with file meta information.
Interestingly, the Created timestamp of $FN was not updated.
Check the record in $ LogFile.
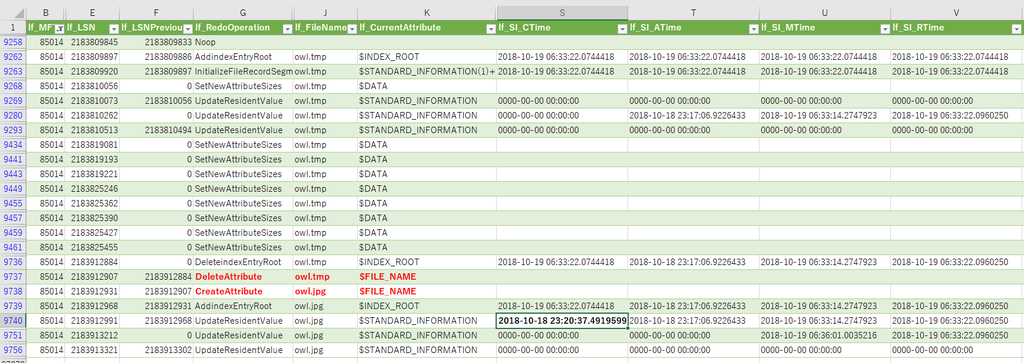
.....If a FILE record already exists, the Created timestamp of $SI is restored and $FN is not restored?
Verification environment: Windows 10 1083
Reference URL:
